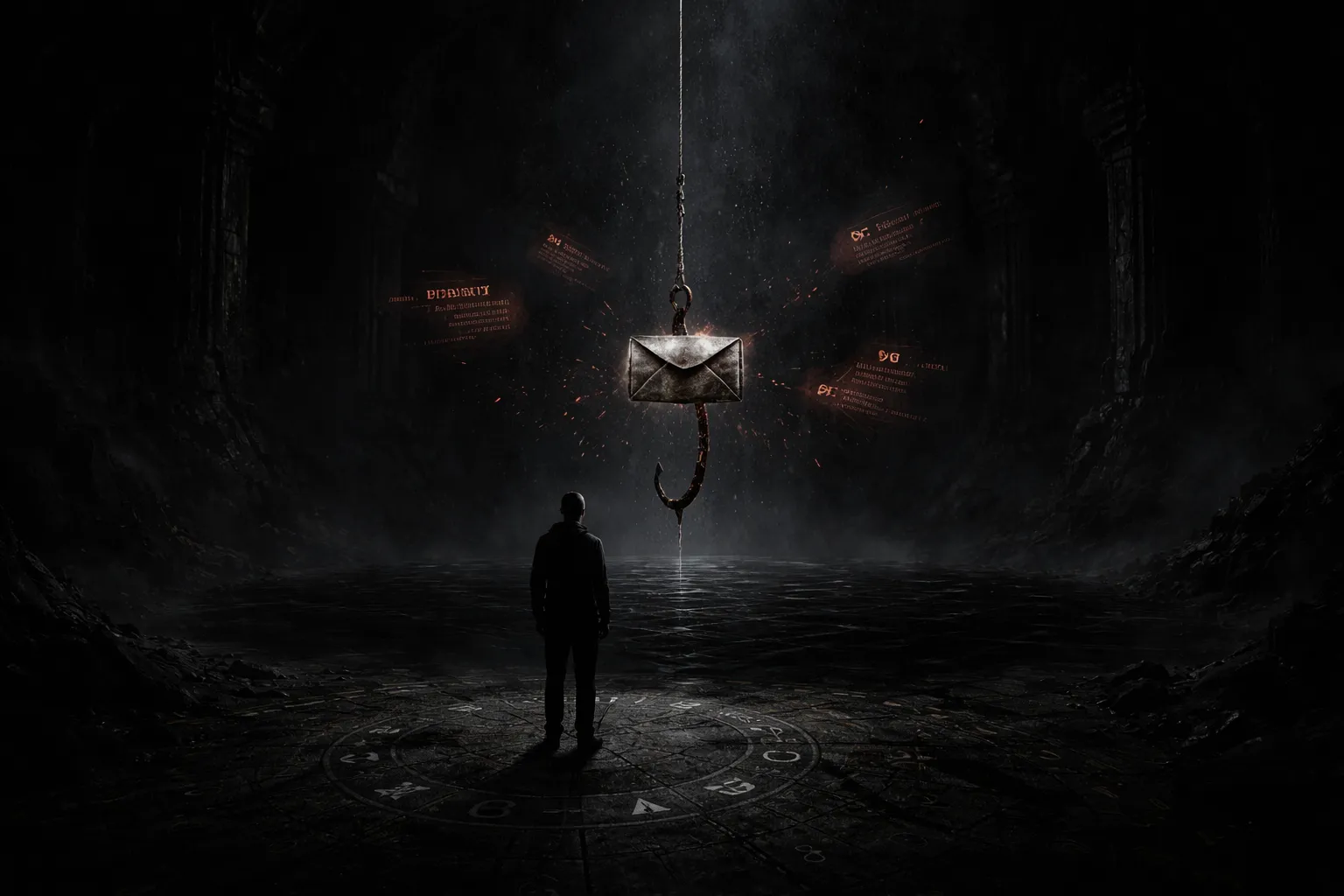
You will run into phishing sooner or later. It might be an email that “needs” you to reset your password, a text about a missed delivery, a phone call that sounds like your bank, or a social media account pretending to be customer support. The channel changes, but the goal stays the same: to push you into doing something that helps the attacker.
It is not just an annoying scam. It is one of the most common ways a cyberattack starts, because it targets the easiest path into any system: a human being.
This guide explains phishing from the ground up, then goes deeper into how modern campaigns work, why spear phishing is so effective, what technical tricks attackers use, how AI is changing the game, and exactly what to do to protect yourself and your organization.
What is Phishing?
Phishing is a social engineering attack where someone pretends to be a trusted person or organization to trick you into sharing sensitive information or taking a risky action. That “trusted” identity could be your bank, a coworker, a government agency, a delivery company, a popular login provider, or even customer support on social media.
Phishing attempts usually try to steal:
Usernames and passwords
One-time codes (SMS codes, authenticator codes)
Credit card details and bank account info
Personal identifiers (national IDs, Social Security numbers, addresses, phone numbers)
Access to email and cloud accounts
Permission to connect an app or approve a login
Sometimes the attacker does not want your data at all. They want your device to run their malware. A phishing message can be the first step of a ransomware infection, a keylogger installation, or a larger cyberattack against a company.
You will also see spearphishing, which is phishing aimed at a specific person or organization. Instead of blasting a generic message to everyone, spear-phishing uses personal context to sound real. A good spearphishing email feels like it was written for you, because in a sense, it was.
Why Phishing Works
Phishing works because it is designed around human decision-making, not around technical vulnerabilities.
Attackers commonly push one or more emotional buttons:
Urgency: “Your account will be locked in 15 minutes.”
Fear: “We detected suspicious activity. Act now.”
Curiosity: “Is this you in this video?”
Greed: “You are eligible for a refund.”
Authority: “This is HR. Review and sign immediately.”
Helpfulness: “Can you quickly pay this invoice?”
Under pressure, people skip verification steps. That is exactly what the phisher wants.
A modern phishing campaign also mimics legitimate communication patterns. It uses branding, tone, logos, and timing that match the real company. Some attackers even A/B test subject lines like marketers do.
This is why it remains one of the most reliable cyberattack methods: it scales well, it is cheap, and it only needs one success.
Many breach investigations still find the human element at the center of incidents. Some industry research has put that number at roughly three quarters of breaches involving human behavior in some way, such as clicking, sharing credentials, or approving access. That is why defenders treat phishing and spearphishing as top-tier cyberattack risks.
A Short History Of Phishing
Phishing is older than many people realize. The term started showing up in the mid-1990s, when attackers used fake emails and sites to steal early internet account credentials. One well-known early wave targeted AOL users.
Since then, it has evolved from clumsy messages with obvious mistakes into campaigns that can look better than the real email newsletters you actually subscribed to.
Two shifts made phishing more dangerous:
Access is easier. Phishing kits and phishing-as-a-service make it simple for low-skill criminals to launch campaigns.
Impersonation is better. AI tools can write natural messages, localize language, and even create realistic voice and video deepfakes.
Today, it is not a single trick. It is a whole ecosystem that supports malware delivery, credential theft, account resale, and larger cyberattack chains.
Why Phishing Is Such A Big Problem
Phishing is a problem because it is efficient. It does not need to break software. It needs you to trust the wrong thing.
Some security research has suggested that the vast majority of targeted attacks start with emails crafted to look legitimate for the recipient. That lines up with what responders see: once a mailbox is compromised, the attacker can pivot to the rest of the environment.
A phishing campaign can
Identity theft
Direct financial loss
Malware infection, including ransomware
Account takeovers
Privacy invasion
Corporate data breaches
Reputation damage
Even strong technical defenses can be bypassed if a user is tricked into handing over credentials or approving access.
Phishing is also a “gateway” technique. A simple email can give an attacker enough access to move deeper into systems and turn a minor incident into a major cyberattack.
Spearphishing is especially dangerous here because it targets the people and roles that can unlock the most access.
Personal Risks Vs Workplace Risks
Personal phishing usually focuses on your money, identity, and personal accounts. The fallout can be painful, but it is often contained to you and your close circle.
Workplace phishing can spill across an entire organization. One mailbox takeover can expose customer data, trade secrets, internal financial systems, and partner communications. That can trigger legal issues, compliance penalties, and long-term reputation damage.
This is why a single successful spearphishing incident can create outsized harm.
Most Targeted Industries And Why They Get Hit
Attackers chase valuable data and reliable payouts. Commonly targeted sectors include:
Social platforms: huge user bases, easy credential reuse
Finance: direct access to funds, high trust in alerts
Ecommerce and retail: shipping lures, payment data, seasonal volume
Payment processors: gateway to many accounts
Technology providers: single sign-on access, broad enterprise reach
Telecom: customer identity data, SIM swap risks
Logistics and shipping: predictable lures and global suppliers
Healthcare: sensitive records and urgent workflows
Travel: loyalty points, urgent itineraries, deal lures
If your job touches payments, account recovery, customer support, or access administration, treat phishing as part of your daily threat model.
Most Impersonated Brands And Seasonal Traps
Attackers often impersonate brands people already trust. Large identity providers and popular consumer platforms are especially attractive because one stolen login can unlock many connected services.
You will also see seasonal spikes:
Holiday shopping brings delivery and “order issue” scams.
Tax season brings refunds and government impersonation.
Back-to-school brings student account and tech support scams.
The exact “top impersonated brands” list shifts year to year, but major tech platforms, ecommerce brands, and shipping companies consistently appear.
Brands frequently impersonated in phishing campaigns include Microsoft, Apple, Google, LinkedIn, Alibaba, WhatsApp, Amazon, Twitter/X, Facebook/Meta, and Adobe. Shipping and travel brands also rise during seasonal spikes.
Attackers pick names you already trust, because trust is the fuel for phishing, and the first step of many cyberattack chains.
In recent brand monitoring reports, Microsoft has repeatedly ranked as the most spoofed brand. Google and Apple are often near the top too.
Retail and shipping brands tend to surge during holidays, when people expect a flood of receipts, delivery updates, and password resets.
How A Phishing Attack Works Step By Step
Even though phishing comes in many flavors, the core process is usually the same. Think of it as bait, hook, and catch.
Step 1: The Bait
The attacker creates a message that looks legitimate. It could be email, SMS, a direct message, or a phone call prompt. They copy:
Visual branding (logos, signatures, formatting)
Sender names that resemble real people
Domains that look close to the real domain
Language and tone that match the organization
For spearphishing, the bait is tailored using details pulled from public sources like LinkedIn, company sites, press releases, and social media.
Step 2: The Hook
The message includes a reason to act. The hook is almost always emotional:
A threat (account suspension, charge, legal issue)
A reward (refund, prize, coupon)
A task (review, approve, sign, pay)
In a workplace attempt, the hook often looks like normal business: a purchase order, a file share link, an “updated” document, or a request from an executive.
Step 3: The Catch
The victim takes action:
Clicks a malicious link
Opens an attachment
Enters credentials into a fake login page
Approves an MFA prompt they did not initiate
Calls a number and shares information
This is the point where the attacker gets credentials, payment, access, or malware execution. That single click can be the start of a serious cyberattack.
The Core Delivery Methods
Most phishing campaigns rely on at least one of these three delivery methods.
Malicious Web Links
A phishing link may send you to:
A fake login page that steals credentials
A real website that redirects you through a malicious chain
A page that triggers a drive-by download
A common campus and enterprise pattern is a “help desk” or “mailbox full” email that links to a page mimicking a popular login provider, often an Office 365-style page. The sender name looks internal, but the true sending domain does not match the organization.
Attackers often hide links behind buttons, images, or “view document” prompts. On mobile, you often cannot preview the destination as easily as you can on desktop, which makes mobile phishing more dangerous.
Malicious Attachments
Attachments can be:
Office documents with malicious macros
PDFs that lure you into clicking embedded links
Compressed files that hide executables
Scripts such as PowerShell payloads in corporate environments
A common pattern is a fake invoice or a shipping notice. The attacker wants you to open the attachment out of habit.
Shipping scams are especially common during peak shopping seasons. Some campaigns have impersonated well-known shippers and asked recipients to print a receipt or label from an attachment, but the attachment carried malware.
Fraudulent Data Entry Forms
Forms are used to harvest:
Logins
Payment details
Personal information
A classic example is a fake tax refund form or a “verify your account” form that copies the look of a government or bank portal. Some scams imitate government tax agencies by offering a refund and then asking the victim to complete a form with personal and financial details.
What Attackers Want From Phishing
Phishing is a tool. Attackers use it for different outcomes.
Direct Financial Theft
Some phishing is simple: trick someone into sending money or sharing card details. This includes gift card scams, fake invoices, and “refund” scams.
Credential Theft And Account Takeover
Stolen logins can unlock email, cloud storage, social media, payroll systems, and customer databases. Email access is especially valuable because it allows password resets for other services.
Malware Delivery
A link or attachment can install ransomware, a remote access trojan (RAT), a keylogger, or spyware. Malware can then spread, steal more data, or encrypt systems for extortion.
Business Email Compromise
In business email compromise (BEC), attackers aim to trick employees into paying invoices or changing payment details. Spearphishing is commonly used to start or support BEC.
Data Harvesting For Future Attacks
Sometimes the first message does not steal money. It steals information that makes future phishing easier, such as org charts, email patterns, project names, and vendor relationships.
Access To AI And SaaS Accounts
A newer angle is stealing access to AI service accounts and other SaaS tools. Compromised accounts can be resold or used to automate more phishing content and expand a cyberattack campaign.
The Major Types Of Phishing Attacks
There are many categories. The differences usually come from the channel used, the level of targeting, or the technical trick involved.
Email Phishing
Email phishing is the most common type. Attackers send messages that look like they come from a trusted organization and push the victim to click a link, open a file, or reply with information.
Email phishing often uses:
Fake domains that mimic real ones
Display-name tricks that hide the true sender
Urgent language to rush the reader
Email phishing can also include spearphishing, whaling, and clone phishing.
Spear Phishing
Spearphishing is targeted phishing. The attacker sends a message designed for a specific person, team, or company.
A spearphishing attacker often researches:
Your name, role, and reporting line
Your colleagues and frequent contacts
Current projects and vendors
Writing style and signature patterns
That context makes spear phishing far more convincing than generic phishing. It also makes it a common starting point for BEC and other high-impact cyberattack campaigns.
A well-known example often cited in security training is the spearphishing directed at Hillary Clinton’s 2016 presidential campaign.
Reporting described Threat Group-4127 (often linked to “Fancy Bear”) targeting more than 1,800 Google accounts using emails tied to a lookalike domain such as accounts-google.com. Attackers used convincing login prompts to capture credentials at scale.
The details matter less than the lesson: spearphishing does not need sloppy tricks. It needs believable context.
Whaling
Whaling is a form of spearphishing aimed at senior leaders and high-privilege roles. The message often looks like it relates to executive tasks: payroll, tax documents, legal requests, wire transfers, and vendor approvals.
An important detail: attackers may target assistants and finance staff because those roles are more likely to process urgent requests.
Clone Phishing
Clone phishing copies a real email that was previously delivered, then swaps a legitimate link or attachment with a malicious one. The attacker may claim it is an “updated” version.
It can be especially dangerous because the email content feels familiar.
Smishing
Smishing is phishing via SMS. It often uses short, urgent messages:
Delivery failure notices
Bank alerts
Account verification prompts
“Your package is waiting” links
Smishing works well because people treat texts as more personal and because it is harder to inspect links on phones.
Vishing
Vishing is voice phishing. The attacker calls you or leaves an automated message and tries to get you to share information, transfer money, or install remote access tools.
Modern vishing risks include caller ID spoofing and voice deepfakes that imitate real people.
In one widely reported case, deepfake-assisted voice impersonation contributed to a fraudulent transfer worth hundreds of thousands of dollars, because the call sounded like a real executive.
Vishing is often paired with email or SMS to create a multi-step cyberattack.
Angler Phishing
Angler phishing happens on social media. Attackers create fake customer support accounts that copy a real brand’s name, handle, and profile picture.
When someone complains publicly, the attacker replies first and sends them to a fake support page or asks for personal info.
Link Manipulation And Typosquatting
Link manipulation is when a URL looks trustworthy but is not. Common tricks include:
Misspellings (typosquatting)
Lookalike subdomains
Internationalized domain name (IDN) spoofing using similar characters
Misleading link text where the displayed text does not match the destination
Example: globalbank.secure.com is not the same as secure.globalbank.com.
Filter Evasion
Some attackers use images instead of text to evade simple filters. Email security has improved, and many systems now analyze images too, but filter evasion still shows up.
Website Forgery And Content Injection
Website forgery can include tricks that alter what you see in the browser, including address bar manipulation. Content injection can happen when attackers place malicious elements on a legitimate site to show you a popup or redirect.
Cross-site scripting (XSS) vulnerabilities can make this worse because you might be on the correct site and still get tricked.
Covert Redirects And OAuth Consent Traps
A covert redirect is when a link looks legitimate but bounces you to a phishing site.
Covert redirects can be hard to spot because the first page in the chain may look normal.
In some scenarios, a victim is browsing a legitimate site and is served a malicious login pop-up through a compromised page, a risky browser extension, or another cyberattack step.
The victim thinks they are authenticating to a trusted service, but the credentials or token go to the attacker.
Sometimes the attacker is not even chasing a password. They want an OAuth token that grants access to email, profile data, contacts, or other permissions.
A related tactic is an OAuth consent trap: a fake “Authorize this app” screen that tricks you into granting permissions. Sometimes the attacker wants an access token more than a password.
Tabnabbing
Tabnabbing targets inactive browser tabs. An attacker triggers a tab to silently redirect, then waits for you to return and log in.
This can be done with browser behavior that allows inactive navigation, and it does not always require JavaScript.
Pharming And DNS Poisoning
Pharming can redirect you to a fake website even if you type the correct domain. One method is DNS cache poisoning, which corrupts how a domain resolves.
Some pharming attacks also involve malware on the device that changes settings or routes traffic.
Phishing Vs Spoofing Vs Pharming
These terms get mixed up, and attackers benefit when people are confused.
Phishing is the overall social engineering play. The attacker tries to trick you into doing something, such as logging in, paying, or installing a file.
Spoofing is usually a disguise technique. Email spoofing, caller ID spoofing, and brand spoofing are methods to look like a trusted sender. Spoofing often supports phishing, but it can also show up in other scams.
Pharming is a redirection technique. It sends you to the wrong place even when you try to do the right thing, such as typing the correct domain. DNS poisoning is one way this happens.
You will also hear people say “hacking” when they mean phishing. A cyberattack can include hacking techniques, but phishing usually starts with manipulation, not exploitation. The attacker is not breaking the lock. They are convincing you to open the door.
The practical takeaway is simple: when you suspect phishing, verify independently. That advice still holds whether the attacker is spoofing a sender, using a phishing kit, or attempting pharming.
Common Phishing Techniques In Detail
This section explains the mechanics that make those types work.
Social Engineering
Social engineering is the umbrella term for manipulating people to get access. Phishing is the most common social engineering approach, and spearphishing is the most targeted form.
Attackers use:
deception (impersonation)
coercion (threats)
bribery (gift cards, rewards)
time pressure (deadlines)
A common mistake is assuming smart people do not fall for phishing. In reality, smart people are busy. That is the vulnerability.
Email Spoofing
The “From” field in an email is not a magical truth serum. Parts of it are just data. Attackers abuse this by:
spoofing the display name so it looks like a trusted contact
spoofing the domain when email authentication is weak
using lookalike domains that differ by one character
Email authentication standards like SPF, DKIM, and DMARC help, but they do not stop lookalike domains or compromised accounts. A spearphishing email from a hacked vendor account can still look perfect.
URL Shortening
Short links hide the true destination. Attackers use this to:
conceal a suspicious domain
make a link look “clean” on mobile
bypass simple filtering that only checks visible text
If you see a shortened link in a security or payment message, treat it as suspicious. Legitimate banks and major platforms rarely need short links.
Malicious Redirects
Redirects are normal on the web. Attackers weaponize them.
A malicious redirect chain may start on a legitimate site, then bounce you to an attacker-controlled page. That makes the link harder to judge, and it can bypass simple “block list” defenses.
Hidden Links
A link can be hidden in:
a logo
a button image
a blank area of an email
This is why “I only clicked the logo” is still a phishing incident.
Double-Barrel Phishing
Double-barrel phishing uses two or more messages to build trust. For example:
Email 1: a harmless message that looks like routine communication.
Email 2: the real phishing link or attachment, referencing Email 1.
This technique is common in spearphishing because it creates a believable thread.
Filter Evasion With Images
Some attackers put the main message inside an image so older filters cannot read it. Many modern defenses use optical character recognition, but image-based phishing still appears, especially in low-budget campaigns.
Website Forgery And Address Bar Tricks
Some phishing pages use scripts to:
show a fake URL overlay
open a new window that mimics the browser UI
manipulate what the user thinks they are looking at
You should also know this uncomfortable truth: even if the page looks perfect, it can still be fake.
SSL And The “Padlock Problem”
HTTPS is important. It protects data in transit.
But attackers can still obtain valid SSL certificates for lookalike domains. You can click the padlock and inspect the certificate to confirm it is issued to the exact domain you expect and is valid, but that still does not prove the site is legitimate. The padlock means the connection is encrypted, not that the site is safe.
Internationalized Domain Name (IDN) Spoofing
IDN spoofing uses characters from other alphabets that look similar to Latin characters. A URL can appear correct at a glance and still be fake.
This matters in phishing and spearphishing because victims often scan, not read.
Tabnabbing With Meta Refresh
Tabnabbing can be done with JavaScript, but it can also be done with browser behavior and HTML meta refresh. You return to a tab you trust, and it is no longer what you left open.
Pharming With DNS Poisoning
Pharming is a phishing technique where you can be redirected even when you type the correct domain.
One method is DNS cache poisoning. Another is malware that changes how your device resolves domains. This is why a phishing defense plan also needs good endpoint security.
Evil Twin Wi-Fi And Man-In-The-Middle Risk
An evil twin hotspot copies a public Wi-Fi name. If you connect, an attacker can observe traffic, inject redirects, and force login prompts.
This is not theoretical. It is a real-world cyberattack pattern in airports, hotels, and conferences.
How AI Is Changing Phishing And Spear Phishing
AI changed phishing in big ways.
AI Makes Messages Sound Human
Grammar mistakes used to be a reliable red flag. Now, AI can generate clean writing in many languages and tones. That means basic “spot the typo” advice is no longer enough.
AI Makes Spear Phishing Scalable
Spearphishing used to be slower because it needed research and customization. AI helps attackers:
Pull details from public data
Mimic writing styles
Reference current events and internal company news
Run multi-step conversations using chatbots
Read stolen email threads and suggest the best way to scam a specific organization, which makes spear phishing feel like it comes from inside the business
This creates hyper-personalized phishing and spearphishing that feels like real internal communication.
AI Makes Vishing Scarier
Deepfake audio makes it easier to impersonate executives, relatives, or support agents. Paired with urgency, this can push victims into fast decisions that lead to a cyberattack.
AI Helps Attackers Adapt
If a victim responds, AI can continue the conversation and adjust tactics in real time. That reduces the chance the victim realizes something is off.
The takeaway is simple: phishing and spearphishing are not getting quieter. They are getting smoother.
How AI Is Advancing Detection
Attackers are not the only ones using AI. Defenders are using it too, especially in email and web security.
Common AI-driven defense approaches include:
Machine learning pattern recognition: models learn what normal email and browsing behavior looks like and flag anomalies.
Real-time threat analysis: links and attachments are evaluated quickly so the window for a cyberattack is smaller.
Advanced email filtering: natural language processing helps spot subtle impersonation and unusual requests, not just known bad keywords.
Visual analysis: some systems analyze emails and web pages visually, similar to how a human notices a fake login page, which helps against brand spoofing.
Behavioral anomaly detection: unusual sign-ins, suspicious clicks, and strange session behavior can trigger step-up authentication or quarantine.
Continuous learning: detection models update as new phishing kits and lures appear.
There is a catch. AI helps, but it is not perfect. Attackers use compromised legitimate accounts, new domains, and multi-step flows to evade filters.
So think of AI defenses as a strong layer, not a replacement for human verification. When a spear phishing message is crafted well, humans still need clear rules and easy reporting to prevent a cyberattack.
How To Verify Suspicious Messages Without Making It Worse
Verification is where most people accidentally help the attacker. The trick is to verify using a path the attacker does not control.
Use A Separate Channel
If the email claims to be from your bank, do not reply to the email and do not call the phone number inside it.
Instead:
open a new browser tab and type the official domain yourself
use a saved bookmark you trust
call the number on the back of your bank card
message the colleague using your normal chat tool, not the email thread
This simple habit breaks a lot of phishing and spearphishing campaigns.
Read URLs Like A Human, Not Like A Robot
You do not need to be technical. You just need to focus on the right part.
The real domain is usually right before the first single slash after
https://.Words before the real domain can be subdomains. Attackers abuse this.
Extra words like
secure,verify,support, andloginare often bait.
If you want a quick sanity check, copy the link text without clicking and paste it into a safe link preview tool or a sandboxed environment used by your security team.
Treat Attachments Like They Are Guilty Until Proven Innocent
Ask yourself:
Did I expect this file?
Does the file type make sense for the sender?
Is the message pushing me to enable macros or “editing”?
A surprising number of ransomware incidents start with someone enabling macros in a document that was never needed.
Use Known Good Sources
There are public services that track known phishing pages. Two well-known examples are PhishTank and OpenPhish. They can help you confirm whether a URL is already flagged.
These resources are not perfect, but they are helpful when you suspect a broad campaign.
Role-Based Verification Playbooks
Some roles get targeted more often. If this is you, make verification a muscle memory.
Finance And Accounts Payable
Verify any payment change request with a known contact method.
Require two-person approval for high-value transfers.
Watch for “new bank details” and “urgent invoice” language.
IT And Help Desk
Never request passwords by email.
Use ticketing systems, not ad hoc email, for software installs.
Treat “security update” attachments as suspicious.
HR And People Ops
Confirm employee data change requests through established HR portals.
Be careful with “policy update” links that ask for logins.
Executives And Assistants
Assume whaling attempts will look polite and plausible.
Use a callback protocol for unusual requests.
If your organization does nothing else, a role-based playbook reduces spearphishing success and prevents a costly cyberattack.
How To Report Phishing
Reporting helps providers and security teams block future campaigns.
Report Phishing At Work
If the message hit your work inbox, report it to your security team first. They can block the sender, remove similar emails from other inboxes, and hunt for related activity.
When you report, include:
the sender address
the subject line
the link or attachment name (do not click it again)
what you did (opened, clicked, entered credentials)
That context helps contain a cyberattack quickly.
Report Phishing As An Individual
If you are in the United States:
Forward phishing emails to the Anti-Phishing Working Group (APWG): [email protected].
Forward phishing text messages to SPAM (7726).
Report the attempt through the FTC’s reporting portal at ReportFraud.ftc.gov.
If the scam impersonated a real company, also report it to that company through their official support channels. Many brands have abuse mailboxes and security pages.
If phishing led to identity theft concerns, use the FTC’s identity theft resources for recovery steps.
Outside the United States, look for your national cybercrime reporting portal or your local consumer protection agency. Reporting is not always satisfying, but it helps defenders map campaigns and take down infrastructure.
Forward phishing emails to the Anti-Phishing Working Group (APWG): [email protected].
Forward phishing text messages to SPAM (7726).
Report fraud through the FTC’s reporting portal (in the United States).
At work, also report the message to your security team. Do not just delete it. Security teams can use headers, URLs, and indicators to protect other employees.
Final Thoughts
Phishing is not going away. It keeps working because it targets how humans communicate and how work gets done.
The good news is that you can beat most phishing with consistent habits, and organizations can reduce risk with layered controls, solid email authentication, and a culture where people report suspicious messages quickly.
Treat phishing as a daily threat, treat spearphishing as a priority risk, and assume every cyberattack will try to start with a message that looks normal. Your job is to make “normal” earn your trust.
- Bit Scriber T1000https://stealthkits.net/author/sp/
- Bit Scriber T1000https://stealthkits.net/author/sp/
- Bit Scriber T1000https://stealthkits.net/author/sp/
- Bit Scriber T1000https://stealthkits.net/author/sp/